Insider Threat Detection
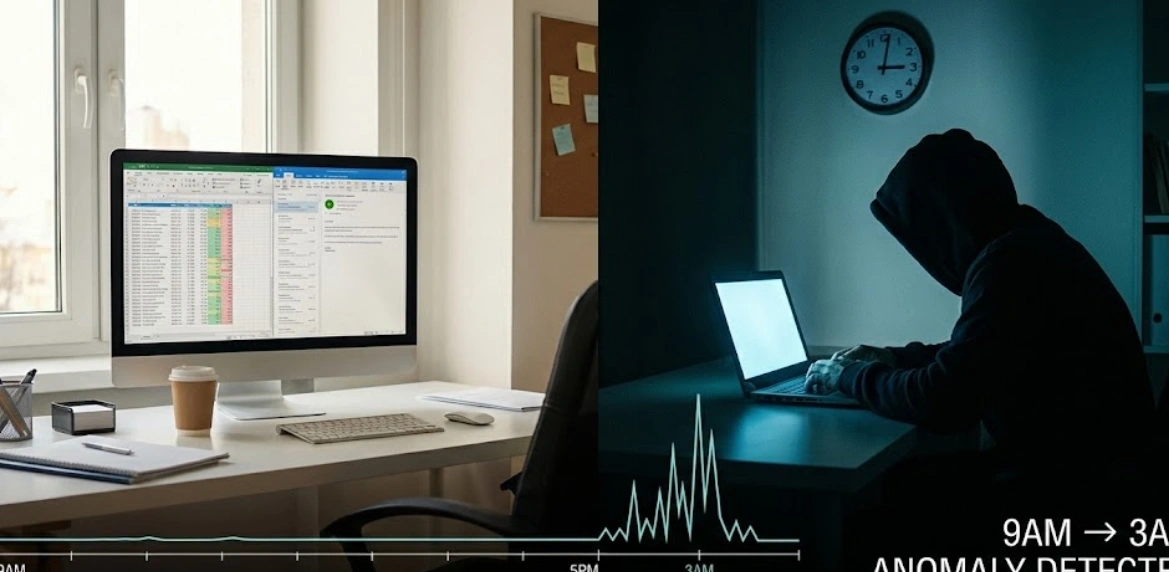
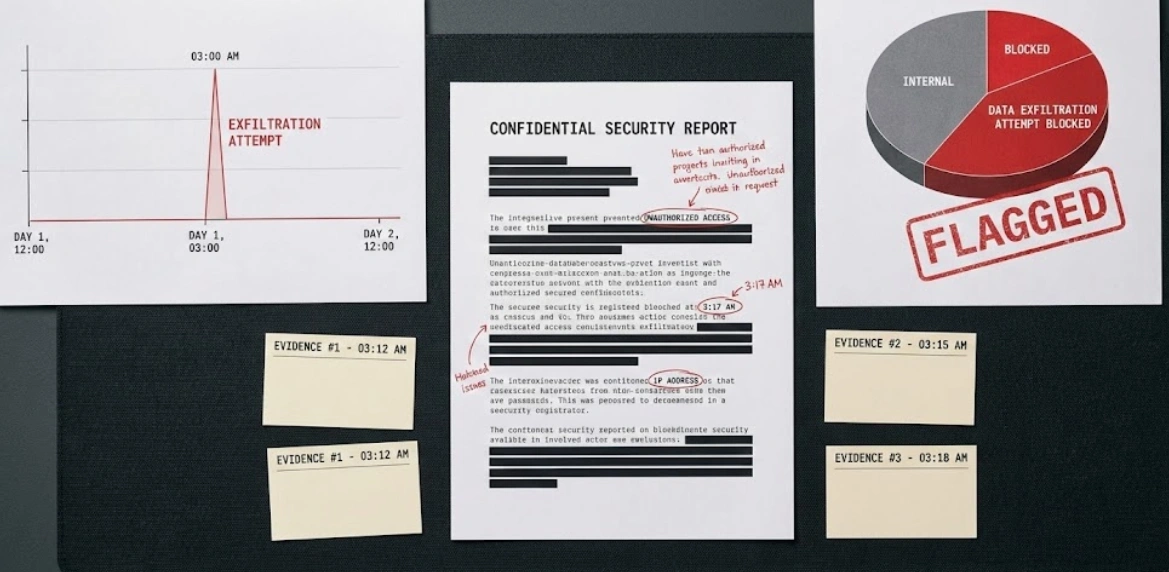
External threats get all the attention, but insiders already have access. Disgruntled employees, compromised accounts, negligent users—different motivations, same result: data loss. Traditional security tools are built to keep bad guys out. They're terrible at noticing when someone who's supposed to be inside is doing something they shouldn't. I built a user behavior analytics platform using Chronicle SIEM and custom ML models. The system learned what normal looked like for every user—what files they access, when they work, what systems they use, who they communicate with. Then we watched for deviations. Employee who normally works 9-5 suddenly logging in at 3am. User who only accesses customer data for their region suddenly pulling records from every region. Someone downloading gigabytes of data right after getting their 2-week notice. The key was reducing false positives. People's behavior changes for legitimate reasons. New project, different team, working late on a deadline. We used context to filter out the noise—correlating behavior changes with HR events, project assignments, calendar schedules. Built a risk scoring system that weighted anomalies by severity and cumulative behavior. One weird thing? Probably nothing. Ten weird things in the same week? Time to investigate. Automated the investigation workflow. When someone hit a risk threshold, system would automatically pull their recent activity, check for data exfiltration attempts, review access history, and package everything for the security team. Caught an employee trying to steal IP before leaving for a competitor. Downloaded entire codebases, design documents, customer lists—all within a 48-hour period. System flagged the behavior, blocked external file transfers, and alerted security before anything left the network. Also caught dozens of compromised accounts that looked like insider activity but were actually external attackers who had stolen credentials. Behavior just didn't match the real user's patterns.
Client
Technology Manufacturer
Deliverables
User behavior analytics
Anomaly detection
Risk scoring
Investigation automation
Year
2024
Role
Security Analytics Lead