Security Engineering in Practice
Real-world lessons from securing cloud infrastructure at scale—what works, what doesn't, and why.
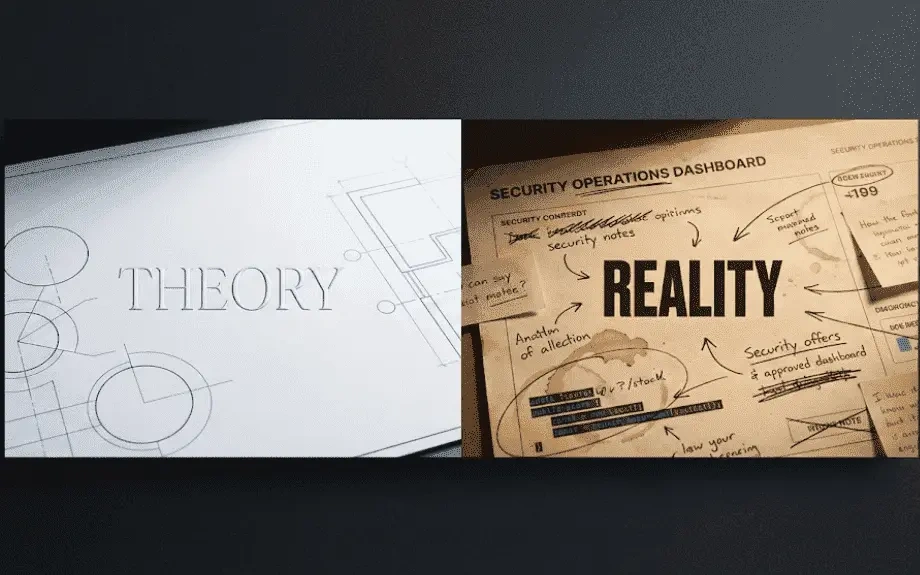
Security engineering isn't what you read about in whitepapers. It's messier, more political, and way more interesting than the theory suggests.
I've spent the last 5 years securing cloud infrastructure. Not building proofs-ofconcept or writing research papers—actually defending production systems that millions of people depend on. Here's what I've learned.
Theory says- Implement zero-trust architecture
Reality- You can't flip a switch and go zero-trust. You've got legacy systems that assume everything inside the perimeter is friendly. Applications that break when you enforce mutual TLS. Teams that need to ship features this quarter, not refactor their entire auth system.
What actually works is progressive zero-trust. Pick one service. Harden it. Learn what breaks. Fix the tooling. Document the patterns. Then expand. Trying to boil the ocean just means nothing gets secured while you're planning.
Theory says- Automate everything
Reality- Automation without understanding is just faster ways to make mistakes at scale. I've seen teams automate incident response and accidentally DDoS themselves by having every alert trigger a restart. Saw another team automate compliance remediation and take down production because a scanner flagged something incorrectly.
Automate the boring stuff first. Log collection. Basic triage. Evidence gathering. The things humans hate doing and machines are good at. Keep humans in the loop for anything that could break things or has business impact.
Theory says- Security should never say no
Reality- Sometimes the answer is no. Not "no because I'm scared of change" but "no because this fundamentally breaks our security model and here's a better way to achieve what you actually need."
The trick is saying no with alternatives. "We can't give you admin access to production, but here's just-in-time elevation that gives you what you need for debugging without permanent blast radius." Now you're solving their problem instead of blocking it.
What actually matters in security engineering
Understanding business context. Security that doesn't understand what the business is trying to accomplish just becomes an obstacle to route around.
Building trust with development teams. If they see security as the team that slows them down, they'll find ways to work around you. If they see security as the team that helps them ship safely, they'll involve you early.
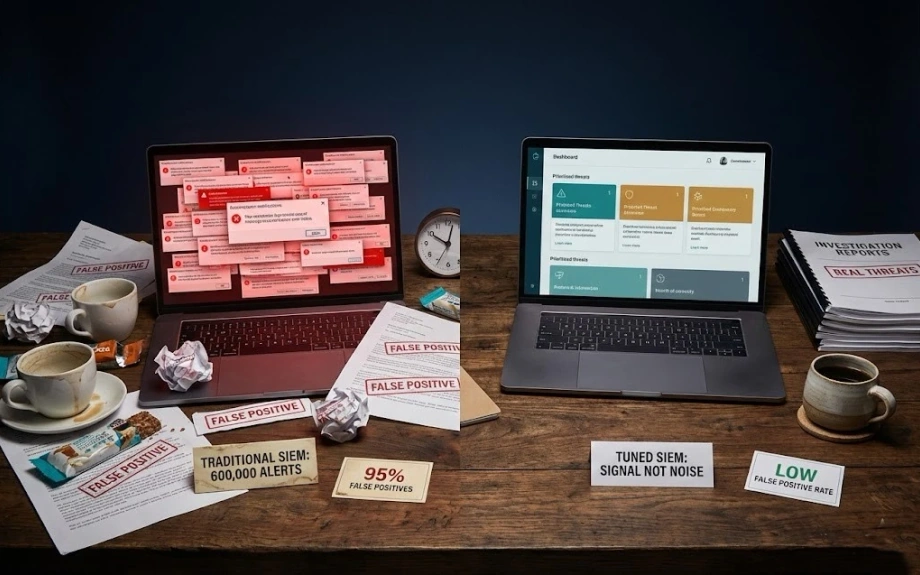
Measuring what matters. Stop counting vulnerabilities. Start measuring: How fast do we detect real threats? How quickly can we respond? Are we blocking actual attacks or just generating alerts?
Being honest about tradeoffs. Perfect security means nothing ships. Zero security means everything's
compromised. We're always making tradeoffs between security, velocity, and usability. Pretending otherwise just means you're making those tradeoffs unconsciously.
The hardest lesson
Security engineering is mostly communication, not technology. The best security architecture in the world is useless if nobody understands it, adopts it, or maintains it.
You can write perfect policies that everyone ignores. Or you can build imperfect systems that people actually use because they make their lives easier. The second option wins every time.
I've seen elaborate security programs fail because they were too complex for the organization to operate. And I've seen simple, pragmatic security programs succeed because they fit how people actually work.
What I'd tell my younger self
Stop trying to build the perfect security program. Start with what's actually breaking and fix that. Build
momentum. Get wins. Earn trust. Then expand.
Your job isn't to prevent every possible attack. Your job is to make the cost of attacking higher than the value gained. Sometimes that's sophisticated AI detection. Sometimes that's just turning on MFA.
Learn to code. Security engineers who can read code, write automation, and build tools get 10x more done than those who just audit and complain.
And finally- security is a team sport. The best security engineering I've seen happens when security is embedded with product teams, not isolated in a separate org throwing requirements over the wall.
That's what actually works in practice. Not what looks good on a conference talk, but what holds up when you're on call at 2am trying to contain an incident with incomplete information and angry stakeholders.
LATEST POSTS
Practical security engineering—what works, what doesn't, and why your SIEM is lying to you.
© RAJ PATHAK
View all posts +