SOAR Automation Platform
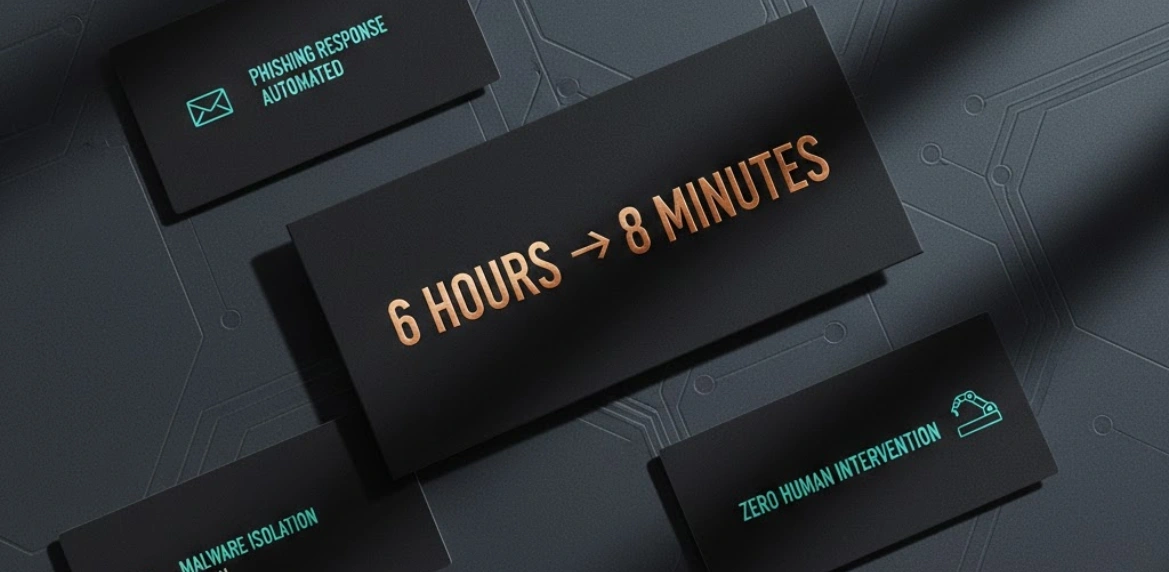
Their incident response was entirely manual. Someone had to read the alert, figure out what it meant, decide what to do, then go execute 15 different steps across 8 different tools. Mean time to respond was over 6 hours, and that's if someone was actually available when the alert fired. Manual response doesn't scale. You hire more people, you get more manual work. And when you're dealing with thousands of potential incidents, you need machines doing the repetitive stuff so humans can focus on the decisions that actually require judgment. I built out a SOAR platform using Google Security Operations that automated the entire initial response workflow. Phishing alert? System automatically retrieved the email, analyzed attachments in sandbox, checked if links were clicked, pulled user's recent activity, and if confirmed malicious, disabled the account and revoked active sessions—all in under 2 minutes without human intervention. Malware detection? System isolated the host, collected forensics, checked for lateral movement, identified patient zero, and generated a full incident report before the analyst even finished reading the initial alert. The trick was making playbooks smart enough to handle variations without being brittle. Used AI to classify incident severity and route appropriately. Low-confidence detections got automated enrichment and human review. High-confidence threats got immediate automated containment. Integrated with everything—EDR, SIEM, IAM, ticketing, comms. The playbooks could take action across the entire stack without needing humans to context-switch between 8 different consoles. Response time dropped from 6 hours to 8 minutes for automated incidents. The team went from fighting fires to actually hunting threats. Analyst burnout dropped significantly because they stopped doing robot work.
Client
Global Insurance Provider
Deliverables
Playbook development
Tool integration
Response automation
Metrics dashboard
Year
2023
Role
Security Automation Lead